Before Bitcoin
Short-form Crypto Fundamentals
-by Infominer
- What’s a Cryptographic Primitive?
- Cryptographic Hash Functions
- Proof of Work in a Nutshell
- Zero Knowledge Proofs
- David Chaum - The Father of Digital Cash
- The Birth of the Cypherpunks
- The Rise of the Cypherpunks
-
Julien Guitton, Bitcoiner 🕶️🍸🍿📈🌕 (@weedcoder)
-
Nick Szabo 🔑 (@NickSzabo4)
Inventors of the most important technologies in Bitcoin: digital signatures and Merkle trees (Merkle), elliptic curve crypto (Koblitz), malicious-fault-tolerant consensus (Lamport), elliptic curve crypto (independent inventor: Miller).
-
Giacomo Zucco [I identify as a bubble collection] (@giacomozucco)
How to spot a crypto-charlatan: somebody posting this 1996 paper as evidence that somebody at NSA was thoroughly describing Bitcoin 12 years earlier (when indeed they were just superficially describing Chaum’s bank-based Ecash 6 years later) https://t.co/hJ5ISK5YFA
- CryptoQuikRead_150 - Why I wrote PGP
- CryptoQuikRead_161 - Bitcoin, The Untold History - article
-
🏷 POS
-
Tuur Demeester (@TuurDemeester)
TIL Proof-of-stake based private currency designs date at least back to 1998. https://t.co/enD2oVnupa
Timelines

https://github.com/peercoin/peercoin/wiki/history-of-cryptocurrency</a>
- Hobbes’ Blockchain Timeline 0.1 — Blockchain, Bitcoin, Distributed Ledgers, Smart Contracts and Cryptocurrencies
- Bitcoin’s Academic Pedigree
- Bitcoin and Markets - Bitcoin History - Timeline of important research and events since 1970.
💲 History of Money
-
Blockchain’s Secret 1,000 Year History
Far from a modern idea, Blockchain, in fact, has a long history tracing all the way back to the tribal villages of the tiny island of Yap in 500AD.
-
Bezant Denier (@bezantdenier)
1.) Published: “Tales of Soft Money — Oceans of Wealth” This article provides eyewitness accounts on the use of seashell money in Africa and in Asia, and also on the logical conclusion of such monetary systems in the face of economic forces. https://t.co/gDDfimILMd
-
Blockchain Mama (@EvolutionCrypto)
April 5th, 1933, federal reserve confiscated all the gold from US citizens. Interesting..
- CryptoQuikRead_075 - Homo Sapiens, Evolution, Money & Bitcoin
- Shelling Out - The Origins of Money
- CryptoQuikRead_176 - Shelling Out - The Origins of Money [Part 1]
- CryptoQuikRead_177 - Shelling Out - The Origins of Money [Part 2]
- CryptoQuikRead_178 - Shelling Out - The Origins of Money [Part 3]
- CryptoQuikRead_179 - Shelling Out - The Origins of Money [Part 4]
- CryptoQuikRead_262 - The Island of Stone Money
- GuysTake_18 - A Story About Booms & Busts
Pre Digital Cryptography
- Pre-Digital Cryptography
- EFF - Crypto Is For Everyone—and American History Proves It
- “GET READY FOR A WORLD CURRENCY” Get Ready for the Phoenix- Economist; 01/9/88, Vol. 306, pp 9-10
- Before Babylon, Beyond Bitcoin: From Money that We Understand to Money that Understands Us
Digital Cryptography
-
The Code Book: The Science of Secrecy from Ancient Egypt to Quantum Cryptography [ϟ]
“Simon Singh offers the first sweeping history of encryption, tracing its evolution and revealing the dramatic effects codes have had on wars, nations, and individual lives. From Mary, Queen of Scots, trapped by her own code, to the Navajo Code Talkers who helped the Allies win World War II, to the incredible (and incredibly simple) logisitical breakthrough that made Internet commerce secure, The Code Book tells the story of the most powerful intellectual weapon ever known: secrecy.”
Hash Algorithms
- History of Hash Algo’s - StackExchange
- New Directions in Cryptography ‘76
- DATA ENCRYPTION STANDARD (DES) approved as a federal standard in ‘76
Public Key Cryptography
-
Publishing a new idea
by Ralph C. Merkle
In the Fall of 1974, as an undergraduate, I enrolled in CS244, the Computer Security course offered at UC Berkeley and taught by Lance Hoffman. We were required to submit two project proposals, one of which we would complete for the course. I submitted a proposal for what would eventually become known as Public Key Cryptography – which Hoffman rejected. I dropped the course, but kept working on the idea.
-
Part 1 — Part 2 about the development of public-key cryptography.

For a more complete version, read: - CRYPTO— how the code rebels beat the government— saving privacy in the digital age -Steven Levy
-
THE OPEN SECRET
—Public key cryptography - the breakthrough that revolutionized email and ecommerce - was first discovered by American geeks. Right? Wrong.
The story of the invention of public key cryptography is a cypherpunk sacred text: In 1976, an iconoclastic young hacker named Whitfield Diffie hooked up with Stanford professor Martin Hellman, and together they devised what experts hailed as the most important development in crypto since the invention of polyalphabetic ciphers during the Renaissance. The duo produced a system that allowed an unlimited number of people to communicate with total privacy.
David Chaum
- Chaum.com
- Everipedia - David Chaum
- Cryptography Legend - David Chaum
- The Birth of Digital Cash
- THE FATHER OF ONLINE ANONYMITY HAS A PLAN TO END THE CRYPTO WAR 2016
- What Everybody Misunderstands About Privacy Pioneer David Chaum’s Controversial Crypto Plan
- How David Chaum’s eCash spawned a Cypherpunk Dream - 2018 - CryptoQuikRead_058
- David Chaum: Godfather of Digital Currency - 2018
Distributed Systems
-
The Origin of Blockchains - What is a Distributed System?
- FLP Impossibility (1985)
- CAP Theorem (1999)
- Paxos (1989)
- Practical BFT (1999)
- Byzantine Paxos (2010)
- Raft (2014)
- PoW - Bitcoin
- The Eureka Moment That Made Bitcoin Possible [ϟ]
Cypherpunks
-
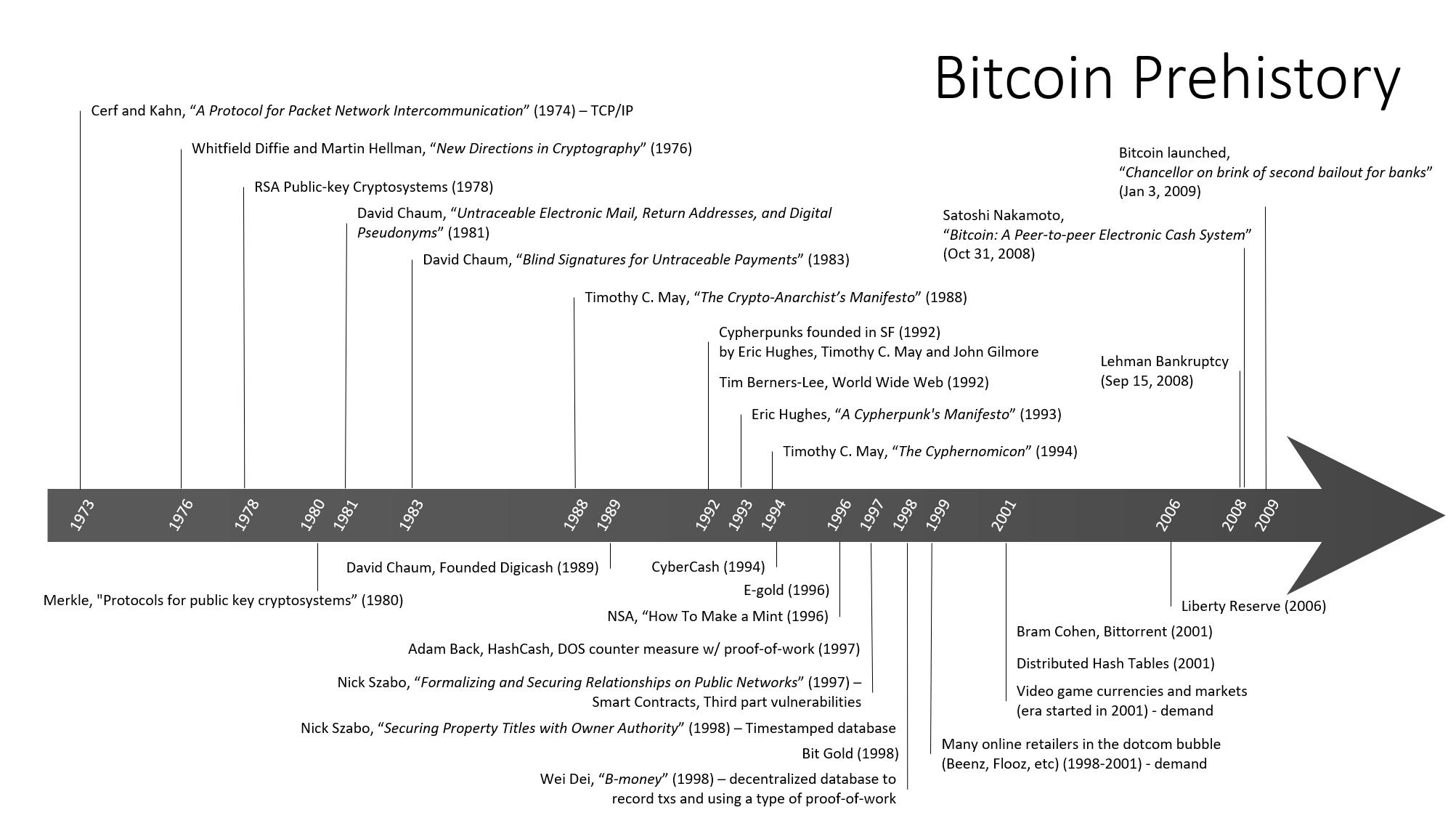
Bitcoin and the rise of the Cypherpunks
- 1980s, Dr David Chaum
- late 1992, Eric Hughes, Timothy C May, and John Gilmore founded cypherpunks
- The Cypherpunks mailing list was formed, and a few months later, Eric Hughes published “A Cypherpunk’s Manifesto“.
“Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn’t want the whole world to know, but a secret matter is something one doesn’t want anybody to know. Privacy is the power to selectively reveal oneself to the world.”
- Notable Cypherpunks:
- Jacob Appelbaum: Tor developer
- Julian Assange: Founder of WikiLeaks
- Dr Adam Back: Inventor of Hashcash, co-founder of Blockstream
- Bram Cohen: Creator of BitTorrent
- Hal Finney: Main author of PGP 2.0, creator of Reusable Proof of Work
- Tim Hudson: Co-author of SSLeay, the precursor to OpenSSL
- Paul Kocher: Co-author of SSL 3.0
- Moxie Marlinspike: Founder of Open Whisper Systems (developer of Signal)
- Steven Schear: Creator of the concept of the “warrant canary”
- Bruce Schneier: Well-known security author
- Zooko Wilcox-O’Hearn: DigiCash developer, Founder of Zcash
- Philip Zimmermann: Creator of PGP 1.0
- In 1997, Dr Adam Back created Hashcash
- Later in 1998, Wei Dai published a proposal for “b-money”,
- Cypherpunks Write Code ϟ
-
Untold History of Blockchain
- Phil Zimmerman creates PGP(‘91), the first publicly available encryption allowing people to communicate using 128-bit encryption and Diffie-Hellman for key management. Zimmerman published PGP code in book form to strengthen its case as freedom ofspeech.
- Open Source software development
- Peer to peer sharing
Pre-Bitcoin Digital Currency
- The Quest for Electronic Currency—Before Bitcoin @infominer
- The Amazing Story of Cryptocurrencies Before Bitcoin ϟϟϟ Digi-Cash—eGold—Bitcoin
-
The Evolution of Digital Cash
“The emergence of digital assets, such as bitcoin, signals a fundamental change in the way value is transferred globally. The concepts of money and value transfer have been evolving since primitive societies adopted shells and stones for monetary exchange, but the concept of digital money has been sought after for as long as there’s been an internet and peer-to-peer networking capabilities to drive its development.”
- DigiCash (1989)
- Hashcash (1997)
- B-money proposal (1998)
- The Bit Gold proposal (1998)
- Reusable Proof of Work (2004)
- A three part story of the tech that paved the way for Bitcoin — eCash (DigiCash), HashCash, Bit Gold.
- Pre-Blockchain Digital Currencies — Digicash, eGold, Beenz, Flooz, Internetcash.
Literature
- Payment mechanisms designed for the Internet
-
DIGITAL CASH AND MONETARY FREEDOM - JON W. MATONIS ‘95 [ϟ]
Much has been published recently about the awesome promises of electronic commerce and trade on the Internet if only a reliable, secure mechanism for value exchange could be developed. This paper describes the differences between mere encrypted credit card schemes and true digital cash, which presents a revolutionary opportunity to transform payments. The nine key elements of an electronic, digital cash are outlined and a tenth element is proposed which would embody digital cash with a non- political unit of value.
- Digital Money: A divine gift or Satan’s malicious tool? 1996 paper, oft cited for early history of virtual currencies
-
NSA: HOW TO MAKE A MINT: THE CRYPTOGRAPHY OF ANONYMOUS ELECTRONIC CASH
- Written in 1996, References two articles written by “Tatsuaki Okamoto” from 1991. [ϟ] - Tatsuaki References
-
What Happened to the Crypto Dream?, Part 1 - part 2 - 2013 Princeton University
- Crypto-history starting from the 80s
Video-Audio
-
History of Cryptocurrencies [Bonus lecture] Princeton - Bitcoin and Cryptocurrency Technologies Online Course
- Bitcoin Prehistory
- Bitcoin History: From the Cypherpunk Movement to JPMorgan Chase
Additional Resources
- P2P Foundation Wiki
- https://nakamotoinstitute.org/literature/
- https://nakamotoinstitute.org/
-
A Survey of Anonymous Communication Channels - 2008
We present an overview of the field of anonymous communications, from its establishment in 1981 from David Chaum to today. Key systems are presented categorized according to their underlying principles: semi-trusted relays, mix systems, remailers, onion routing, and systems to provide robust mixing. We include extended discussions of the threat models and usage models that different schemes provide, and the trade-offs between the security properties offered and the communication characteristics different systems support.
- UNITED NATIONS COMMISSION ON SCIENCE AND TECHNOLOGY FOR DEVELOPMENT - 17-21 May 2010, Geneva, Switzerland: Technology Driven Universal Currency Improvements and Innovations in Existing Financial Mechanisms
Today close to 90% of our financial transactions have a computer-only reality, no coins, and no bills. But the bits and bytes reflect national currencies defined as paper money equivalent. The next level in the increasing abstraction of credit, risk and value is to mint a currency natively defined as a string of bits. Bitdefined currency features the utmost flexibility in storage and movement, as well as in reflecting value, risk, and credit distribution.
- btcmanager.com/tag/history
Edit this page
Social Share
Twitter Facebook LinkedIn Reddit
Tips Welcome
| Bitcoin | DOGE |
|---|---|
| 1A1DZfw4VgpHCgnMjnmfDnMjddKf8xdYbd | DQKkzfJjqnXUD8Z7C3e84vKzvghPe9dXSa |
 |
 |